

Fraud & Security Center
REPORT FRAUD OR SUSPICIOUS ACTIVITY
- You believe your account information has been stolen or compromised
- There are transactions you don’t recognize on your account
- Your check book, purse, wallet, smartphone, and/or ID was lost or stolen
- Lost or stolen credit, debit, or ATM card
- You need to stop a payment/check
| Check your account frequently and immediately report any transactions you do not recognize. |
Resources To Help You Avoid Fraud
The National Bank of Indianapolis is dedicated to maintaining the highest standards of security and privacy for the Bank and for our clients. We take special steps to safeguard our clients’ accounts and personal information. However, fraud is increasingly prevalent, and scammers are smarter than ever before. We’re here to provide information that can help protect you before fraud occurs and help you access important resources if you have been a victim of fraud.

PERSONAL AND
PRIVATE BANKING
CLIENT SECURITY
- Secure online and mobile banking
- Text account balance alerts
- E-statements
- Privacy – The National Bank of Indianapolis will not share or disclose SSN, account numbers or other private information with third parties.
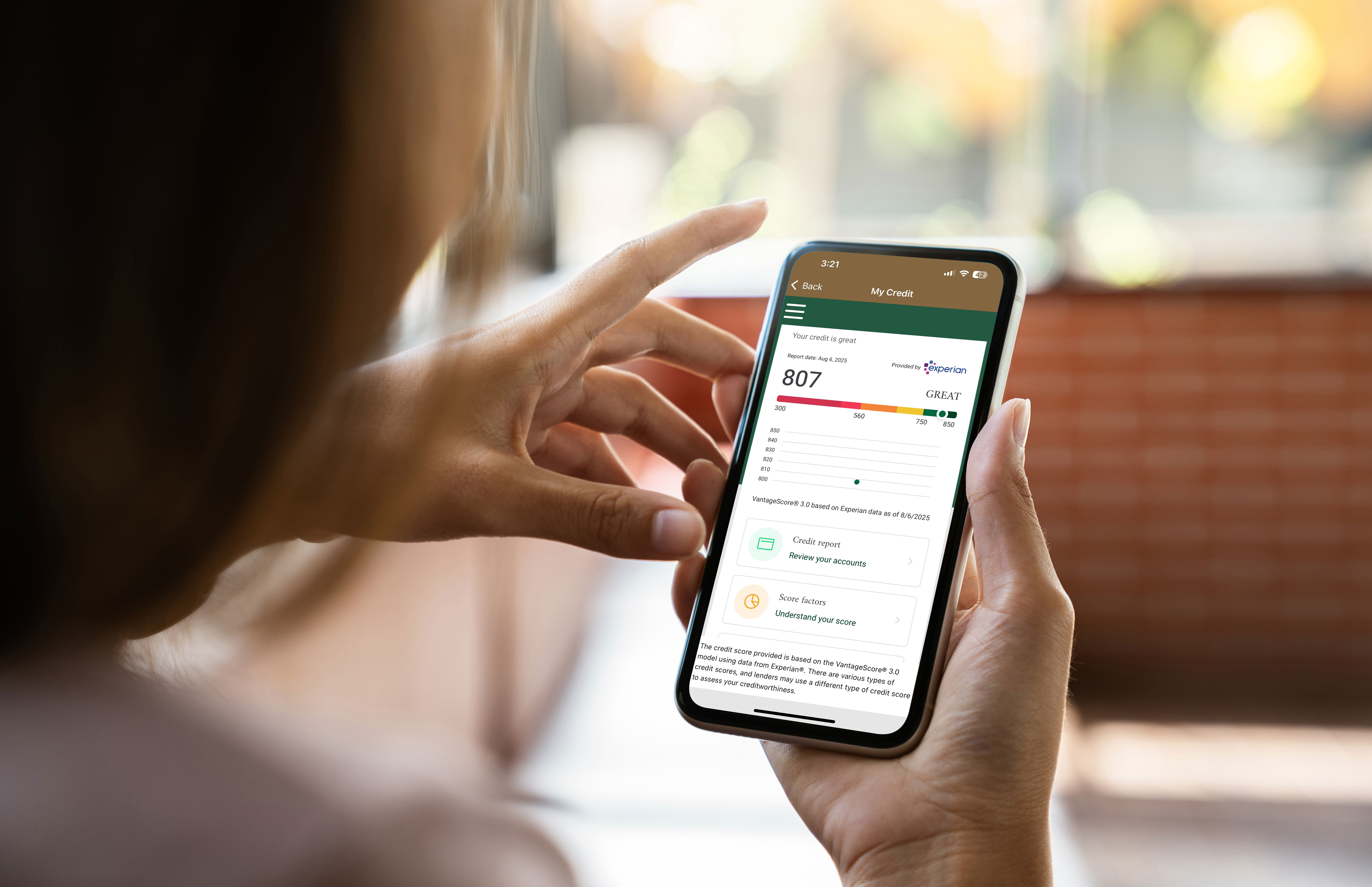
MONITOR YOUR CREDIT
Clients of The National Bank of Indianapolis have access to “My Credit” on our mobile app. Through “My Credit” clients can access their credit report as well as other features to help monitor and manage their credit.
Speak to your banker or call 317-261-9000 for assistance navigating “My Credit” on the app.
IMPORTANT TIPS TO PROTECT YOURSELF
Avoiding fraud requires a cautious, careful, and proactive approach. There are certain steps you can take to help keep yourself secure. While not all-encompassing, these are effective tips for staying ahead of scammers.
- Never send account numbers, passwords, your social security number, PIN, or other confidential information by email, over text messages, or direct messages on apps or social media platforms.
- Frequently monitor your accounts by using online or mobile banking. Report any unauthorized or questionable charges as soon as possible.
- Avoid using public Wi-Fi or other unsecured connections when using online or mobile banking, paying bills, or performing other secure transactions.
- Never respond to unsolicited calls, emails, text messages, or direct messages on apps or social media platforms requesting financial or confidential information.
- Never click links that come from unsolicited emails, text messages, or direct messages on apps or social media platforms.
- Do not reply to a call or call back a phone number sent over a text or email.
Above all, remain calm. Most scam calls or messages create a sense of urgency (example: a text demanding payment on a past-due bill) that pressures the potential victim into acting quickly or irrationally. Stop and think. When in doubt, reach out to your Banker at The National Bank of Indianapolis or a friend or family member you trust for advice before you do anything else.
If you have been the victim of Identity Theft or are concerned you may be, follow these steps:
- Call the Fraud Department. Explain that someone has stolen your identity. Ask them to close or freeze the accounts. Once an account is frozen, no one can add new charges unless you agree to them.
- Change logins, passwords, and PINs on all your accounts.
- To place a fraud alert, contact one of the three credit bureaus. That company must communicate your fraud alert to the other two. Fraud alerts are free and will make it harder for someone to open new accounts in your name.
- Visit Experian Fraud Alert or call 1-888-397-3742
- Visit TransUnion Fraud Alert or call 1-800-680-7289
- Visit Equifax Credit Report or 1-888-766-0008
- Get your free credit reports from Equifax, Experian, and TransUnion. Go to AnnualCreditReport.com or call 1-877-322-8228.
- Review your reports. Make note of any account or transaction you don’t recognize. These details will help when you report the theft to the FTC and the police.
- Go to IdentityTheft.gov and click “Get Started”. Include as many details as possible.
- Based on the information you enter, IdentityTheft.gov will create your Identity Theft Report and a personal recovery plan.
Indiana residents can freeze their credit free of charge. A credit freeze also known as a security freeze, is a consumer right provided by Indiana law. Placing a credit freeze on your credit reports can block an identity thief from opening a new account or obtaining credit in your name. A credit freeze keeps new creditors from accessing your credit report without your permission. If you activate a credit freeze, an identity thief cannot take out new credit in your name, even if the thief has your SSN or other personal information, because creditors cannot access your credit report.
There are many different types of scams out there, luckily there are some common red flags. If your answer is “yes” to any of the following questions, you may be dealing with a scammer:
- Payment by gift card: Is someone or some business requesting that you make payments by gift card? Even if they claim to be someone you know, it may be a scam.
- Has someone called you claiming to be your grandchild or loved one who is in jail and needs money? AI technology has made it easier and easier to fake real voices and photos. Think before you speak or respond.
- Have you received an unexpected letter in the mail, an email, or text message stating you won a lottery? Was an unsolicited link provided? Are you being asked to cash a check and send back a portion of the funds to pay for taxes or attorney fees? Are you being asked to input your account number, PIN, or other personal information to receive payment? It may be scam.
- Have you received a letter, email, text message or direct message on social media or other apps with words like Income, Investment, Credit, Billion, or Free prominently featured? These are the top words used in cyber scams.
- Have you recently sold something online, and received an over-payment? Are you being asked to send a portion of that back? It may be a scam.
- Have you recently received a pop-up window on your computer stating it is infected with a virus? Even if the ad states it is Microsoft, this is likely a scam.
Elder adults experience billions of dollars in financial losses resulting from fraud annually. It is also one of the least reported types of fraud due to shame, being uncertain of who to turn to, or simply wanting to put it in the past.
Fraudsters often target older adults who they consider to be wealthy, isolated, less familiar with technology, challenged by disability, or generally more vulnerable.
Elder fraud occurs most often when scammers impersonate a person in a position of trust or extort funds through fear tactics. In grandparent schemes, another example of a financial crime targeting seniors, a scammer impersonates the victim’s grandchild requesting financial aid in a crisis. Fraudsters play on emotions and with the rise of AI technology’s ability to mimic voices and images, it can be easy to be deceived.
- An older family member or friend appears frantic for money.
- The person is making uncharacteristic financial decisions and/or is hard to contact.
- The person is withdrawing large amounts, attempting to make large wire transfers, or is seeking to purchase a large number of gift cards.
While Elder Fraud is about targeting the elderly, the attics that can be used to avoid many other scams are applicable here. Speak to your friends and family about the risks of elder fraud. Communicate regularly and check in on those who may need extra support.
FBI
Office of the Comptroller of Currency
Office for Victims of Crime
It is a best practice to block unsolicited calls, emails, text messages and direct messages from people and organizations you do not know. In addition to blocking and deleting these messages, reporting them and telling your friends and family members is a great way to help inform others. Protect yourself and share your experiences with others.
- Secure online and mobile banking
- Text account balance alerts
- E-statements
- Privacy – The National Bank of Indianapolis will not share or disclose TIN or EIN, account numbers or other private information with third parties.
- Fraud Prevention Services (additional cost may apply) – use these tools to only allow authorized transactions to affect your account:
- ACH Blocks and Filters
- Positive Pay
- Educate your employees:
- How to spot phishing scams and impostor email scams
- Best practices for keeping confidential or banking information secure, both within the office, and when emailing
- Question requests that just don’t seem right, such as unusual wire or funds transfers requests or invoices
- Use secure passwords
- If possible, use a dedicated, secure workstation for banking or other confidential activity.
- Ensure your anti-virus protection is sufficient and up to date.
- Monitor you accounts daily. If you notice suspicious activity, contact us immediately. Failure to do so could result in you being liable for fraud losses.
- Contact us for more information on keeping your business safe and secure.
Ways to avoid fraud and known scams and schemes are always evolving. The National Bank of Indianapolis regularly provides information on developing protection techniques through our Diamond Insights blog as well as other topical financial guidance.



